Eric Adams’ Seized Devices-Only Source Of Specific Electronic Evidence
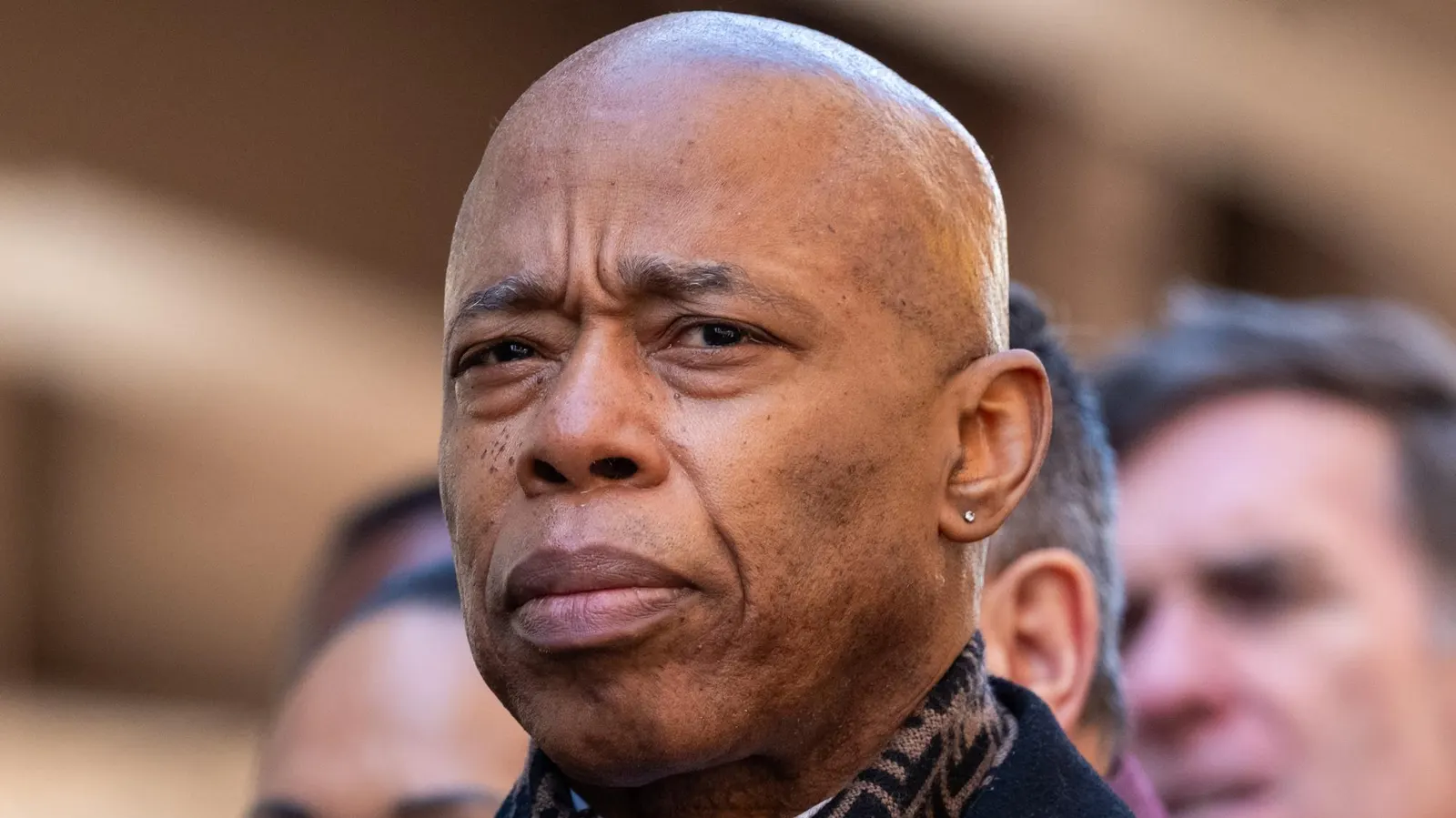
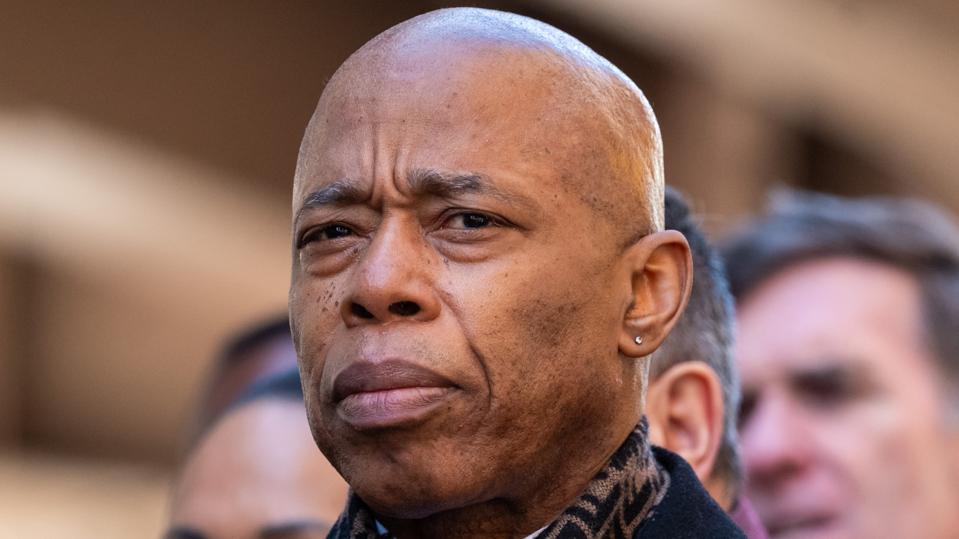
NEW YORK, NEW YORK - MARCH 01: New York City Mayor Eric Adams attends a memorial for the 30th ... [+] anniversary of the killing of teenager Ari Halberstam on the Brooklyn Bridge on March 01, 2024 in New York City. In 1994 a Lebanese-born terrorist fired at a van carrying 15 Hasidic teenagers in what was one of the city’s worst pre-9/11 terror incidents. Halberstam was killed while several others were wounded. (Photo by Spencer Platt/Getty Images)
The recent seizure of New York City Mayor Eric Adams' digital devices by the FBI represents a significant moment in the ongoing federal investigation into his campaign fundraising practices.
When law enforcement seizes digital devices like smartphones, tablets and computers, it typically indicates that investigators believe these devices hold evidence that may corroborate information found in paper documents or digital records from remote sources, such as cloud-based file storage and service providers. More importantly, physical devices contain evidence that exists nowhere else.
Online Data Is Limited
While online service providers may retain deleted files in the trash or deleted folders for a short period, those records are often purged after a certain timeframe, usually on a rolling basis. Once deleted, users can also manually empty the trash folder, making those files and communications irretrievable and truly deleted from the online platform. This stands in stark contrast to physical devices.
Physical Devices Contain Data That Exists Nowhere Else
With access to smartphones, tablets and computers, digital forensics experts can recover extensive amounts of deleted data from the physical storage areas on the devices themselves.
This data includes not only the actual messages, files and records but also other types of data a user is completely unaware of and has no access to when using their devices. With these additional digital artifacts, experts can piece together a more complete understanding of the who, what, when, where and why in a case.
For example, these artifacts might include information such as when specific applications were accessed, who was involved in communications and when those exchanges occurred, even if actual message content has been erased.
Additionally, location data from the device can place individuals at specific locations during key moments, providing investigators with a detailed timeline of the user's activities.
Truly deleted data from online sources can be a relatively simple task, but erasing data from a physical device is extremely difficult and requires a correctly performed factory reset for mobile devices and full disk wiping utilities for a computer.
The seizure and examination of physical devices represent an escalation in almost every investigation. Our online activities can provide investigators with a wealth of information, but this pales compared to what can be recovered from physical devices using modern digital forensics technology.